Zama Pt. II: FHE Operations
Blockscout now supports FHE operations with Zama, enabling visibility into encrypted smart contract execution and homomorphic compute activity.

Zama’s work on Fully Homomorphic Encryption (FHE) has introduced a different model for how smart contracts can operate onchain. Instead of exposing all inputs and outputs, contracts can compute directly on encrypted data while still producing results that are verifiable by the network.
That idea becomes tangible through applications like confidential tokens, where balances and transfer amounts are no longer publicly visible. But encrypted assets are only one part of the picture. Underneath every confidential interaction sits a layer of computation that is also happening on encrypted data.
Blockscout explorers now surface this layer directly through FHE operations and tags, making it possible to inspect how confidential smart contracts execute without revealing the underlying values.
What Are FHE Operations?
In a traditional smart contract, computation happens on plaintext values. If a contract checks a balance, adds two numbers, or evaluates a condition, those inputs and outputs are visible onchain.
With Zama’s approach, those same operations happen on encrypted equivalents. A balance check, for example, becomes a comparison between encrypted values. A transfer becomes a series of encrypted additions and subtractions.
Each of these steps is recorded as an FHE operation.
From the outside, a transaction might still look like a simple interaction with a contract. Internally, however, it can involve a sequence of encrypted operations that determine how state changes are applied. These operations are emitted through logs and processed by the protocol’s coprocessors, which handle the underlying computation.
What Blockscout adds is a way to surface and structure this activity so it can be explored.
Bringing Encrypted Execution into the Explorer
The integration parses FHE-related logs and indexes them alongside standard transaction data. This allows the explorer to present a view of encrypted execution that was previously difficult to inspect in a structured way.
On supported networks, transactions now include information about the FHE operations they triggered. This includes both a high-level summary and a more detailed breakdown for those who want to go deeper.
Rather than changing how transactions work, this adds context around what is already happening under the hood.
Transaction-Level Visibility
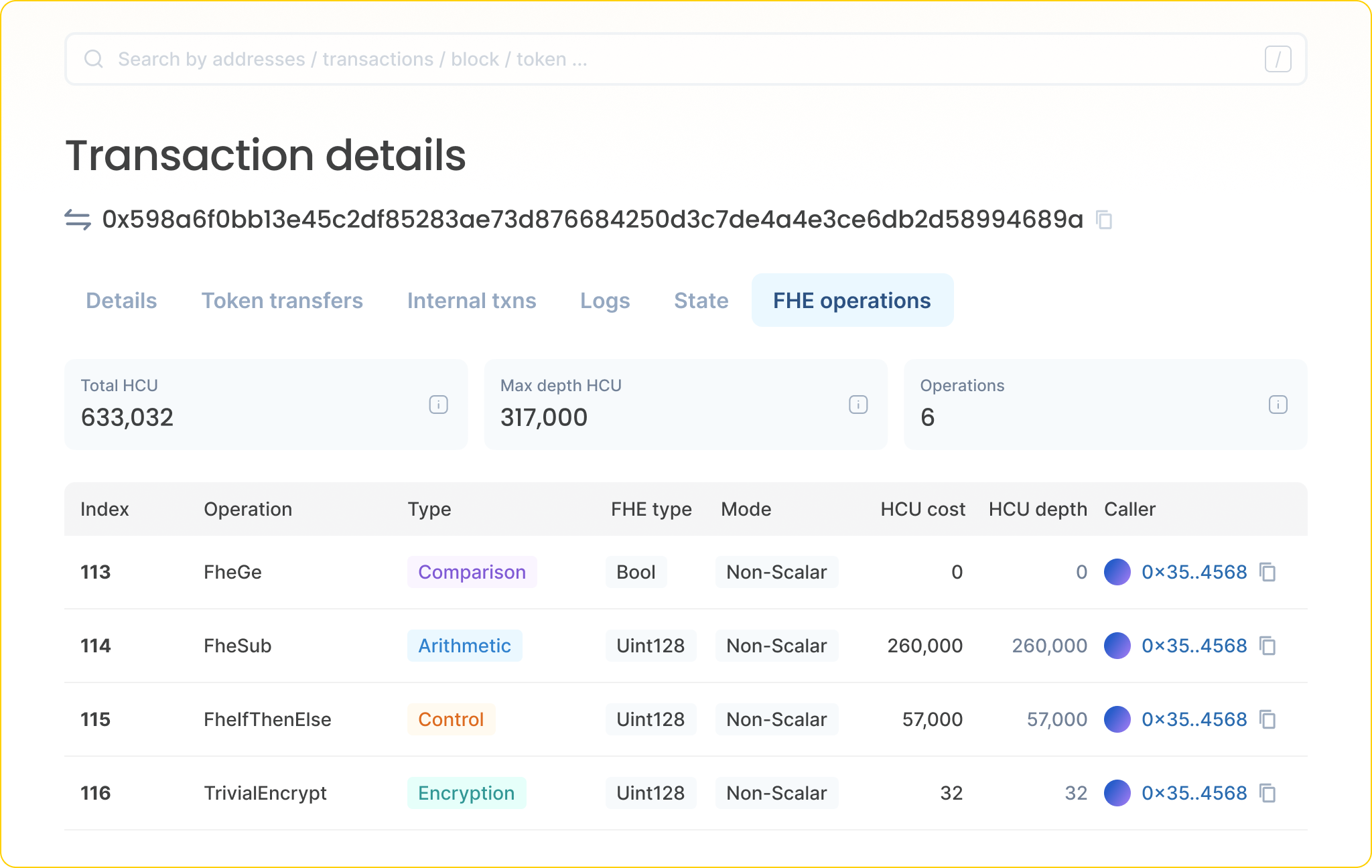
Transaction pages now include an FHE operations count and associated computation metrics. This gives a quick sense of how much encrypted processing is involved in a given interaction.
For simpler interactions, the number of operations may be relatively small. More complex contracts, especially those implementing financial logic, tend to involve a larger sequence of encrypted steps.
This view helps distinguish between different types of activity without needing to inspect raw logs manually.
Inspecting FHE Operations via API
For developers, Blockscout exposes a dedicated endpoint:
/api/v2/transactions/:transaction_hash/fhe-operations
This returns an ordered list of operations associated with a transaction, along with metadata such as operation type, caller, and computation metrics.
Access to this data makes it easier to build tooling around confidential applications. It also provides a foundation for analyzing how encrypted computation behaves across different contracts and use cases.

Measuring Encrypted Computation
To make this activity easier to reason about, Blockscout explorers now show Homomorphic Compute Units (HCU) as a metric.
HCU reflects the computational effort required to perform FHE operations, similar in spirit to how gas reflects EVM execution costs. By surfacing total HCU and related metrics at the transaction level, the explorer provides a way to compare and understand the relative complexity of encrypted interactions.
As confidential applications become more common, this type of measurement becomes increasingly important for both performance analysis and user experience.
Identifying FHE-Enabled Contracts
Another part of the integration is automatic tagging of contracts that perform FHE operations.
When a contract is detected to be using encrypted computation, it is labeled accordingly within the explorer. This makes it easier to identify which parts of a network are already adopting confidential execution patterns.
Over time, this should help map out the growth of FHE-enabled applications and provide a clearer view of where this model is gaining traction.
Interpreting Encrypted Activity
One of the challenges with confidential systems is balancing privacy with observability. If everything is hidden, it becomes difficult to understand what a system is doing. If everything is visible, privacy is lost.
FHE introduces a middle ground.
The underlying values remain encrypted, but the structure of computation is still accessible. You can see that a contract performed a series of operations, how complex those operations were, and how they relate to a transaction, without exposing the sensitive data involved.
For developers, this makes it possible to reason about contract behavior and debug issues in a more familiar way. For users, it provides a level of assurance that interactions are behaving as expected, even when the details are private.
For institutions and more advanced use cases, this model is particularly relevant. It allows systems to maintain confidentiality while still offering verifiability and auditability at the protocol level, something that has traditionally required trade-offs between private and public infrastructure.
Connecting Back to Confidential Tokens
This release builds on Blockscout’s earlier support for confidential tokens based on the ERC-7984 standard.
If you want a deeper look at how encrypted balances and transfers work, you can read the first part here:

That integration focused on how assets can exist in an encrypted form. FHE operations extend that visibility to the computation layer, showing how those assets are actually processed within smart contracts.
Together, these features provide a more complete view of confidential applications, from token activity to execution logic.
Continuing the Exploration
Confidential computation is still an emerging area, and the tooling around it is evolving quickly.
As more developers experiment with FHE-based contracts, we can expect to see more complex patterns of encrypted execution, along with new ways of analyzing and visualizing them.
Blockscout’s role here is straightforward: even as data becomes private, the system should remain understandable. By surfacing both confidential assets and the operations behind them, explorers can continue to serve as a reliable interface for navigating what is happening onchain.